Posted by:
admin
9 years, 9 months ago
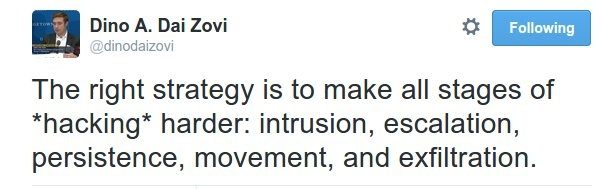
Another tweet struck me for it's common sense and truth:
To me, this is defense-in-depth defined. I will also point out that the "two effective security technologies that stand the test of time" (firewalls and two-factor authentication) can be make these stages harder for attackers:
- Implementing two-factor authentication for remote access will make intrusion much more difficult.
- Implementing two-factor authentication for privileged accounts will make escalation much more difficult.
- Implementing two-factor authentication at your outbound proxy will make exfiltration much more difficult.
We have seen a big increase in the use of two-factor authentication for remote access (thanks to regulations like PCI, often). I think we're about to see a big increase in two-factor authentication for privileged access management both for systems administrators and third-party access. We have recommended using pam_radius to implement two-factor authentication for Sudo for a long, long time. Now with more tools for privileged access management available we will see this in the Windows world. It's well past time. In addition to thwarting escalation, such a setup would make detection easier and therefore movement and persistence more difficult as well.
I don't think we will see too much 2FA for out-bound access except for organizations with high-value IP. Organizations should be able to implement it quickly - in case they think there has been an intrusion.
You don't want to create new identity silos when doing this. Make sure that your authentications run through your directory even if you have to setup a RADIUS server to make it happen. (With the possible exception of vendors that you don't want in your active directory.)
The hardest part is most likely not the implementation, but convincing users and management that it's worthwhile to avoid being the next OPM.
Share on Twitter Share on Facebook
Recent Posts
- Blast-RADIUS attack
- The latest WiKID version includes an SBOM
- WiKID 6 is released!
- Log4j CVE-2021-44228
- Questions about 2FA for AD admins
Archive
2024
2022
- December (1)
2021
2019
2018
2017
2016
2015
2014
- December (2)
- November (3)
- October (3)
- September (5)
- August (4)
- July (5)
- June (5)
- May (2)
- April (2)
- March (2)
- February (3)
- January (1)
2013
2012
- December (1)
- November (1)
- October (5)
- September (1)
- August (1)
- June (2)
- May (2)
- April (1)
- March (2)
- February (3)
- January (1)
2011
2010
- December (2)
- November (3)
- October (3)
- September (4)
- August (1)
- July (1)
- June (3)
- May (3)
- April (1)
- March (1)
- February (6)
- January (3)
2009
- December (4)
- November (1)
- October (3)
- September (3)
- August (2)
- July (5)
- June (6)
- May (8)
- April (7)
- March (6)
- February (4)
- January (427)
2008
- December (1)
Categories
- PCI-DSS (2)
- Two-factor authentication (3)
Tags
- wireless-cellular-mobile-devices (7)
- Two-factor authentication (10)
- Wireless, cellular, mobile devices (6)
- NPS (1)
- Phishing and Fraud (111)
- Active Directory (1)
- pam-radius (3)
- privileged access (2)
- Cloud Security (10)
- Mutual Authentication (60)
- Web Application Authentication (1)
- Authentication Attacks (99)
- pci (50)
- Security and Economics (97)
- WiKID (133)
- pam (2)
- VPN (1)
- Installation (2)
- RADIUS Server (1)
- Open Source (64)
- Tutorial (2)
- Strong Authentication (35)
- Information Security (137)
- Transaction Authentication (13)
- Miscellaneous (100)
- Linux (2)
- transaction-authentication (6)
- Two Factor Authentication (254)